Best Cross-Chain Interoperability Protocols
Best Cross-Chain Interoperability Protocols | Secure & Scalable Bridges
The blockchain landscape has undergone a radical transformation. What began as a series of isolated digital islands—Bitcoin, Ethereum, and early Layer 1 networks—has evolved into a sprawling archipelago of specialized ecosystems. However, as the number of networks grows, so does the problem of fragmentation. Without a way for these networks to communicate, liquidity remains trapped, developers must rebuild the same tools for every chain, and users are forced to navigate a maze of complex manual transfers.
Cross-chain interoperability is the solution to this fragmentation. It refers to the ability of different blockchain protocols to communicate, share data, and transfer value without intermediaries. In 2025, interoperability is no longer a luxury; it is the backbone of Web3 growth. It enables a “multi-chain future” where the underlying network is abstracted away, allowing users to interact with decentralized applications (dApps) as easily as they browse the traditional internet.
This article provides a deep dive into the mechanics of cross-chain communication, the primary players in the space, and the security frameworks that will define the next decade of decentralized finance and data exchange.
Why Cross-Chain Interoperability Matters
The necessity of interoperability stems from the inherent limitations of a single-chain world. In a siloed environment, an asset on Ethereum cannot easily participate in a high-speed DeFi protocol on Solana or a gaming ecosystem on Avalanche. This lack of connectivity creates several critical friction points that stifle innovation.
Breaking Liquidity Fragmentation
Liquidity is the lifeblood of finance. When assets are scattered across dozens of chains, market depth decreases, leading to higher slippage and less efficient price discovery. Interoperability protocols unify these pools, allowing capital to flow to where it is most productive. This is particularly vital for DeFi (Decentralized Finance), where cross-chain lending and yield aggregation rely on the seamless movement of assets. Without it, a surplus of capital on one chain cannot meet the demand for borrowing on another.
Enhancing User Experience (UX)
For mass adoption to occur, the “crypto” part of the experience must become invisible. Users should not need to know which chain their assets are on or how to manually bridge tokens. Interoperability protocols enable “one-click” experiences where a user can buy an NFT on one chain using funds from another, drastically lowering the barrier to entry for non-technical users. The goal is “Chain Abstraction,” where the user interacts with an interface, and the backend handles the multi-chain routing.
Use Case Expansion
Beyond simple asset transfers, interoperability unlocks complex use cases:
-
Cross-Chain Governance: DAOs can allow members to vote on proposals regardless of which chain their governance tokens are held on, preventing the fragmentation of community voice.
-
Universal NFTs: Gaming items can be moved between different games on different networks, preserving their metadata, history, and value across the metaverse.
-
Enterprise and Institutional Adoption: Large financial institutions require systems that can talk to both private enterprise ledgers (like Corda or Hyperledger) and public blockchains to settle trades or manage tokenized real-world assets (RWAs).
How Cross-Chain Interoperability Protocols Work
To understand how these protocols function, it is helpful to look at the mechanisms they use to move data and value across the “gap” between blockchains. Because blockchains are designed to be “closed systems” that only trust their own internal state, communicating with an outside chain requires a sophisticated verification process.
1. Asset Transfer Models
Most bridges utilize one of three primary methods to move value:
-
Lock-and-Mint: This is the most common model. A user “locks” their original asset in a smart contract on the source chain (e.g., ETH on Ethereum). The bridge then “mints” an equivalent wrapped token (e.g., wETH) on the destination chain. When the user wants to return, the wrapped tokens are burned, and the original assets are unlocked.
-
Burn-and-Mint: In this model, the protocol actually destroys the asset on the source chain and issues a native version on the destination chain. This is often used for tokens that have native implementations on multiple networks, such as USDC or certain governance tokens.
-
Atomic Swaps: This involves a peer-to-peer exchange where two users trade assets on different chains simultaneously. If one party fails to complete their end of the bargain, the transaction is cancelled for both, ensuring no one loses funds.
2. Message Passing vs. Asset Transfer
While early bridges were focused solely on moving tokens, modern protocols focus on General Message Passing (GMP). This allows a smart contract on Chain A to “call” a function on Chain B. This is the difference between sending a box (asset) and sending an instruction (data). For example, a user could trigger a swap on a DEX on Chain B without ever leaving the interface of Chain A.
3. Verification Mechanisms
The most critical part of the process is how the destination chain knows that the event on the source chain actually happened.
-
Relayers and Oracles: These entities monitor the source chain and relay the proof of a transaction to the destination chain.
-
Validators: Some protocols use a dedicated network of nodes that vote on the validity of cross-chain messages. This is an external consensus layer.
-
Light Clients: These are high-security models where the destination chain actually runs a “miniature” version of the source chain’s consensus to verify proofs directly on-chain. This is often called “client-side verification.”
Types of Cross-Chain Interoperability Solutions
The ecosystem can be categorized based on how the connection is established and the level of trust required by the user.
Cross-Chain Bridges
Bridges are applications specifically designed to move assets. They are often “point-to-point,” meaning they connect two specific chains. While efficient, they often create “wrapped assets” which carry the risk of the bridge protocol itself.
Messaging Protocols
These are the “postal services” of the blockchain world. They don’t just move money; they move any kind of data. Protocols like LayerZero or Axelar fall into this category. They provide the infrastructure that other dApps build on top of.
Layer 0 Protocols
Layer 0s are the foundational layers. Instead of building a bridge between two existing blockchains, Layer 0s provide a framework where many blockchains can be built from the start to be compatible. Polkadot and Cosmos are the leaders here.
Native Interoperability Blockchains
Some new Layer 1 blockchains are built with built-in “bridge” modules. These allow them to interact with major networks like Ethereum or Bitcoin natively, without needing a third-party intermediary.
| Approach | Trust Level | Scalability | Flexibility |
| External Validators | High Trust required | High | High |
| Light Clients | Low Trust (Secure) | Low (Expensive) | Medium |
| Liquidity Networks | Medium Trust | Medium | Low |
Key Factors to Evaluate Cross-Chain Protocols
When evaluating which protocol to use for a project or where to move significant capital, several “North Star” metrics should be considered.
Security Model and “Trust-Minimization”
The most important factor is the security model. Does the protocol rely on a centralized group of people (a multisig) or a decentralized network of validators? Ideally, a protocol should be “trust-minimized,” meaning you don’t have to trust a person or a company; you only have to trust the mathematics of the code.
Decentralization
A protocol is only as strong as its weakest link. If a cross-chain protocol claims to be decentralized but only has five validators, it is vulnerable to collusion or regulatory pressure. True decentralization requires a diverse and geographically distributed set of nodes.
Speed and Finality
Blockchains have different “finality” times—the time it takes for a transaction to be considered irreversible. A bridge must wait for finality on the source chain before acting on the destination chain. If a protocol is too fast, it risks moving funds that might later be “rolled back” on the source chain, leading to a loss of collateral.
Developer Friendliness
For an interoperability protocol to succeed, developers must want to build on it. This requires comprehensive documentation, SDKs (Software Development Kits), and a standardized API. Chainlink’s success in the oracle space was largely due to its “plug-and-play” nature for developers.
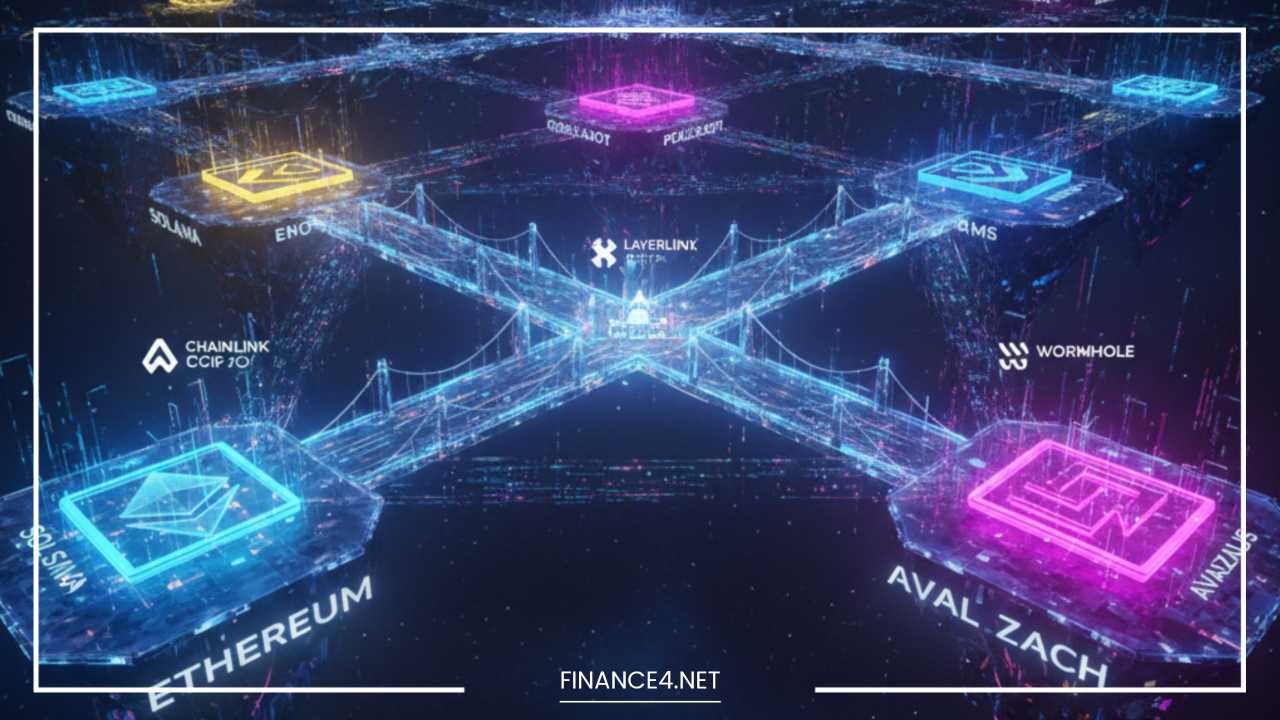
Best Cross-Chain Interoperability Protocols (Main Section)
The following protocols represent the “state of the art” in 2025. Each has chosen a different trade-off between security, speed, and ease of use.
1. Polkadot (The Relay Chain Model)
Polkadot is a “Layer 0” protocol that connects a network of specialized blockchains called Parachains.
-
Mechanism: At the center of Polkadot is the Relay Chain, which handles the security and consensus for the entire network. Parachains “rent” a slot on this Relay Chain.
-
The XCM Standard: Polkadot uses the Cross-Consensus Message Format (XCM). Because all parachains share the same security umbrella of the Relay Chain, they can talk to each other with a level of trust that is impossible between unrelated chains like Bitcoin and Ethereum.
-
Use Cases: Polkadot is ideal for “app-specific blockchains” where a developer wants to build a custom chain for a specific purpose (like privacy or high-frequency trading) while remaining connected to a larger ecosystem.
2. Cosmos (The IBC Protocol)
Cosmos is often called the “Internet of Blockchains.” Its primary contribution is the Inter-Blockchain Communication (IBC) protocol.
-
Mechanism: Unlike Polkadot, Cosmos does not have a central security layer. Each chain (or “Zone”) is sovereign and maintains its own validators. IBC acts as a standardized communication protocol that allows these sovereign chains to exchange data.
-
Adoption: IBC has seen massive adoption, powering ecosystems like Osmosis, Celestia, and dYdX. It is widely considered the most robust “light client” based interoperability standard in existence.
-
Strengths: It offers maximum freedom for developers. You can build your own chain and join the Cosmos network without needing permission from a central authority.
3. Chainlink CCIP (The Enterprise Standard)
The Cross-Chain Interoperability Protocol (CCIP) is Chainlink’s entry into the messaging space. Given Chainlink’s dominant position in the oracle market, CCIP was immediately adopted by major players.
-
Security Focus: CCIP introduces the Risk Management Network. This is an independent set of nodes that monitors the CCIP network for any unusual activity. If it detects a potential hack, it can unilaterally pause the bridge.
-
Enterprise Utility: CCIP is designed with traditional finance (TradFi) in mind. It allows banks and institutions to move tokenized assets across different private and public blockchains with a level of security that meets regulatory standards.
-
Mechanism: It uses a simplified “Lock and Mint” or “Burn and Mint” interface that developers can trigger with a few lines of code.
4. LayerZero (Omnichain Interoperability)
LayerZero has become famous for its “Omnichain” concept—the idea that a token or dApp should exist on all chains at once.
-
Ultra-Light Nodes (ULN): Traditional light clients are expensive to run on chains like Ethereum. LayerZero solves this by using an Oracle and a Relayer. The Oracle sends the block header, and the Relayer sends the proof. When these two match, the transaction is verified.
-
Flexibility: LayerZero allows developers to choose their own combination of oracles and relayers, giving them control over their security-to-cost ratio.
-
Stargate Finance: LayerZero’s flagship bridge, Stargate, was the first to solve the “bridging trilemma,” allowing for native asset swaps with instant guaranteed finality and unified liquidity.
5. Wormhole (The Ecosystem Connector)
Wormhole is a generic message-passing protocol that connects over 30 different blockchains, including non-EVM chains like Solana and Sui.
-
The Guardian Network: Wormhole is secured by a set of 19 “Guardians,” which are some of the largest and most reputable validator companies in the crypto space. They observe transactions and sign “Verified Action Approvals” (VAAs).
-
Reach: Wormhole is the primary bridge for the Solana ecosystem. It facilitates a massive volume of transfers between the high-speed Solana network and the liquidity-rich Ethereum network.
-
Evolution: Following a major hack in 2022, Wormhole has implemented some of the most rigorous security practices in the industry, including a massive bug bounty and global “circuit breakers” to stop suspicious flows.
6. Axelar (The Decentralized Overlay)
Axelar provides a decentralized network and tools that help dApp developers with cross-chain communication.
-
Mechanism: Axelar is its own blockchain built on the Cosmos SDK. It uses a decentralized set of validators to verify messages and assets. When you send a message via Axelar, the Axelar validators reach a consensus that the event happened before passing it to the destination.
-
General Message Passing: Axelar’s GMP allows developers to build “Interchain dApps.” For example, a user could lend collateral on one chain and have it immediately reflected in their credit limit on a completely different chain.
-
Ease of Use: Axelar provides a “Squid” router that allows for one-click swaps between any two tokens on any two supported chains.
Security Risks and Challenges in Cross-Chain Bridges
Despite the technological advancements, cross-chain infrastructure remains the “soft underbelly” of the crypto world. Because bridges hold massive amounts of locked collateral, they are attractive targets for hackers.
The “Honey Pot” Problem
A bridge contract is essentially a massive “honey pot” of assets. If an attacker finds a single vulnerability in the smart contract logic of the bridge on the source chain, they can mint unlimited wrapped tokens on the destination chain and drain the liquidity.
Centralization and Multisig Risks
Many early bridges were secured by a “multisig”—a wallet that requires, for example, 5 out of 9 people to sign a transaction. If an attacker manages to compromise 5 of those people (via phishing or social engineering), they have total control over the bridge. This was the cause of the famous Ronin Bridge hack.
Finality and Reorgs
A “reorg” happens when a blockchain’s history is rewritten slightly. If a bridge processes a transfer before the source chain transaction is truly finalized, and then a reorg happens, the original assets might be “un-sent” while the wrapped assets on the destination chain remain. This creates “unbacked” tokens, which can collapse the value of the bridge’s assets.
Complexity Risk
The more chains a protocol supports, the more complex the code becomes. Each blockchain has its own virtual machine (EVM, SVM, Move, etc.) and its own security assumptions. Managing the “edge cases” for 30+ different chains is a monumental task that increases the surface area for bugs.
Cross-Chain Use Cases Across Industries
We are moving into an era where interoperability is no longer a technical niche but a business requirement.
Decentralized Finance (DeFi) 2.0
In the next phase of DeFi, users won’t “bridge” their assets. They will use Cross-Chain Yield Aggregators that automatically move their funds to whichever chain offers the highest return, accounting for gas fees and risks. Cross-chain lending will allow a user to keep their Bitcoin (wrapped) on one chain as collateral while borrowing stablecoins on a Layer 2 to pay for real-world expenses.
Gaming and the Metaverse
Imagine an RPG where your character is an NFT on Ethereum, your gold is a token on Polygon, and the game’s actual logic runs on a high-speed chain like Solana. Interoperability protocols allow these three components to interact in real-time. If you sell your sword in the game, the funds are automatically sent to your wallet on the appropriate chain without you needing to sign multiple manual bridge transactions.
DAOs and Governance
Currently, most DAOs (Decentralized Autonomous Organizations) are tied to a single chain. This excludes users on other networks. Interoperability allows for Universal Voting. A DAO can snapshot the holdings of its members across ten different chains and aggregate them into a single voting result.
Supply Chain and Logistics
Enterprise blockchains are often private. However, to settle a payment, they must interact with public financial networks. An interoperability protocol can act as a “secure gatekeeper,” allowing a private supply chain ledger to trigger a payment in a public stablecoin (like USDC) only when a specific shipment is verified as delivered.
Future of Cross-Chain Interoperability
The future of the space can be summarized in one word: Invisibility.
Layer 0 Evolution
We will likely see a consolidation of Layer 0 protocols. As Cosmos and Polkadot mature, they will likely find ways to connect their respective ecosystems, creating a “Meta-Network” that covers the majority of the blockchain space.
Unified Liquidity Layers
Instead of every bridge having its own separate pool of money, we are seeing the rise of Unified Liquidity Layers. These are decentralized protocols that allow any bridge to tap into a shared pool of assets, making cross-chain transfers cheaper and faster.
Zero-Knowledge Proofs (ZK-Bridges)
ZK technology is the “Holy Grail” of interoperability. A ZK-bridge allows a source chain to generate a mathematical proof that a transaction happened. The destination chain can verify this proof instantly and with 100% certainty, without needing to trust any validators or oracles. This removes the human element from the security equation.
Standardization
Just as the internet converged on the TCP/IP protocol, the blockchain industry is working toward standardization. Efforts like the Blockchain Interoperability Alliance are working to create a set of rules that all chains can follow, making the “translation” between networks much simpler.
Final Thoughts
The “Blockchain Wars” of the last decade—where networks competed to be the “Ethereum Killer”—are effectively over. The winner is not a single chain, but the Interchain. The future belongs to the protocols that can bridge the gaps between these diverse ecosystems safely and efficiently.
When choosing a protocol, whether as a developer or an investor, remember that interoperability is a spectrum. On one end, you have high-speed, high-flexibility messaging like LayerZero and Wormhole. On the other, you have the high-security, foundational architectures of Polkadot and Cosmos. In the middle, you have enterprise-grade solutions like Chainlink CCIP.
As we move toward “Chain Abstraction,” the complexities of bridging will fade into the background. Users will simply interact with applications, and the robust, secure, and scalable bridges described in this article will be the invisible “pipes” that power the global decentralized economy. The era of the digital island is over; the era of the connected world has arrived.