How to Manage Bridging Credentials for DAOs
How to Manage Bridging Credentials for DAOs | Secure Cross-Chain Access Guide
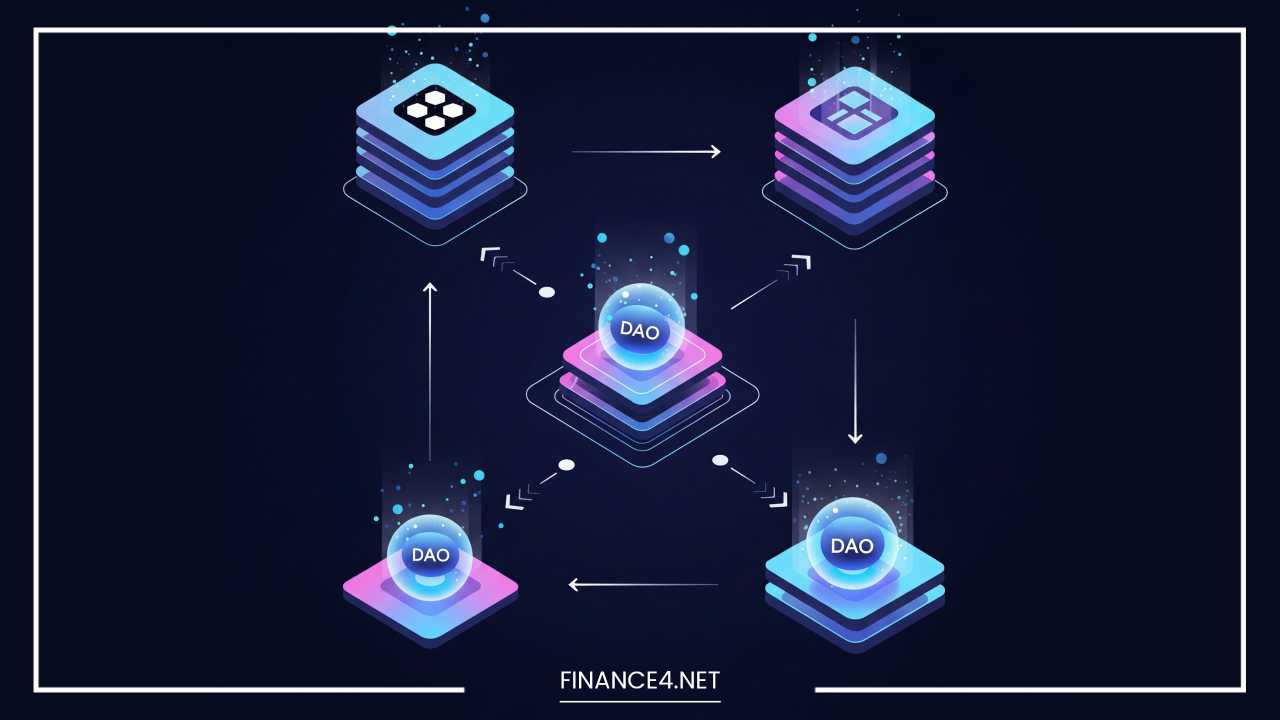
The advent of Decentralized Autonomous Organizations (DAOs) has ushered in a new era of collaborative governance, empowering communities to make collective decisions on a global scale. However, as DAOs mature and their operations expand across various blockchain networks, a critical challenge emerges: how to effectively manage and bridge credentials. This issue, often overlooked in the initial fervor of decentralization, is fundamental to the scalability, security, and true decentralization of DAOs.
The Fragmented Landscape of DAO Credentials
Traditional DAOs often operate on a single blockchain, where membership, voting power, and reputation are typically tied to a wallet address holding specific governance tokens or NFTs. This monolithic approach, while simple, creates silos. As DAOs seek to interact with other protocols, participate in multi-chain ecosystems, or leverage specialized functionalities on different chains, the fragmentation of identity and credentials becomes a significant hurdle.
Imagine a DAO member who has built substantial reputation on Ethereum through consistent contributions, proposal voting, and active participation. If this DAO decides to launch a sub-DAO on Solana for a specific high-throughput application, how does that member’s established reputation on Ethereum translate to their standing in the new Solana-based sub-DAO? Without a robust bridging mechanism, they might start from scratch, undermining the value of their past contributions and hindering seamless cross-DAO collaboration.
This fragmentation manifests in several key areas:
- Identity: A user’s identity is often tied to a specific wallet address on a given blockchain. Interacting with multiple chains necessitates managing multiple wallet addresses, leading to a disjointed and cumbersome user experience.
- Reputation: Reputation, built through on-chain activity, contributions, and historical engagement, is locked within the confines of a single chain. Bridging this reputation is crucial for establishing trust and influence across different DAO ecosystems.
- Voting Power: Governance tokens, which confer voting power, are typically native to one blockchain. Moving these tokens across chains, or ensuring their equivalent representation, is essential for maintaining consistent governance.
- Access Control: Credentials that grant access to specific resources, roles, or permissions within a DAO are often chain-specific. Cross-chain access control is vital for composite DAOs or those that interact with multi-chain dApps.
- Compliance & KYC/AML: As regulatory scrutiny increases, DAOs may need to incorporate compliance checks (Know Your Customer/Anti-Money Laundering). Bridging these verifiable credentials securely and privately across chains is a complex yet necessary endeavor.
The Imperative of Bridging Credentials
The inability to effectively bridge credentials stifles the growth and interoperability of the DAO ecosystem. It creates friction for users, limits the composability of decentralized applications, and ultimately hinders the realization of a truly interconnected Web3. Addressing this challenge is not merely about technical solutions; it’s about fostering a more cohesive, efficient, and equitable decentralized future.
The necessity for bridging credentials arises from several factors:
- Enhanced Interoperability: DAOs are increasingly looking to leverage the strengths of different blockchains. For instance, a DAO might use Ethereum for core governance and high-value assets, while utilizing a Layer 2 solution or a faster chain like Solana or Polygon for more frequent, lower-value transactions or specific dApp functionalities. Seamless credential bridging is the connective tissue.
- Improved User Experience: For users, managing multiple identities and re-establishing reputation on every new chain is a significant barrier to entry and participation. Bridging credentials streamlines this process, creating a more unified and intuitive Web3 identity.
- Scalability and Efficiency: By distributing operations across multiple chains, DAOs can enhance scalability and reduce transaction costs. Bridging credentials ensures that governance and membership remain consistent despite this distributed architecture.
- Risk Mitigation: Diversifying operations across chains can help mitigate risks associated with network outages, congestion, or security vulnerabilities on a single blockchain.
- Cross-DAO Collaboration: The future of Web3 envisions a network of interconnected DAOs collaborating on larger initiatives. Bridging credentials enables DAOs to recognize and interact with members and their qualifications from other DAOs, fostering true “metagovernance.”
- Reputation Portability: The concept of “on-chain reputation” is gaining traction. This reputation, built through verifiable actions and contributions, should be portable across chains to truly reflect a user’s standing in the decentralized world.
Approaches to Bridging Credentials
Bridging credentials for DAOs requires a multifaceted approach, combining cryptographic primitives, novel token standards, and thoughtful architectural designs. Here are some promising avenues:
Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs)
DIDs and VCs, standards proposed by the W3C, form the bedrock of self-sovereign identity.
- Decentralized Identifiers (DIDs): DIDs are globally unique, resolvable identifiers that do not require a centralized registry. They are designed to be controlled by the individual or entity that owns them, rather than by a third party. A DID can be associated with multiple blockchain addresses and off-chain data, serving as a universal identifier for a DAO member.
- Verifiable Credentials (VCs): VCs are tamper-proof digital certificates issued by an “issuer” (e.g., a DAO, a university, or a reputation service) to a “holder” (the DAO member). These credentials can attest to various attributes, such as membership, voting history, skills, or even KYC verification. The holder can then present these VCs to a “verifier” (another DAO, a dApp) who can cryptographically verify their authenticity and integrity without relying on the issuer directly.
How they bridge: A DAO member could hold a DID, and various DAOs could issue VCs to this DID, representing their contributions, roles, or governance power on different chains. When interacting with a new chain or DAO, the member simply presents the relevant VCs associated with their DID, and the new entity can verify these credentials regardless of their original chain of issuance. This creates a portable, self-sovereign identity layer that transcends individual blockchains.
Soulbound Tokens (SBTs)
Inspired by Vitalik Buterin, SBTs are non-transferable tokens permanently linked to a specific wallet. Unlike governance tokens that can be bought and sold, SBTs represent an immutable record of a user’s identity, achievements, or affiliations.
- Use Cases for DAOs:
- Membership Badges: A DAO could issue SBTs to members who have completed a certain onboarding process or demonstrated a commitment to the DAO’s mission.
- Contribution Recognition: SBTs can serve as verifiable proof of contributions (e.g., proposal writing, code development, community management) within a DAO, building a reputation score that cannot be transferred or sold.
- Role-Based Access: SBTs can grant specific roles or permissions within a DAO, such as “Core Contributor” or “Grants Committee Member,” which are tied directly to the individual’s identity.
- Sybil Resistance: By associating unique, non-transferable SBTs with real-world identities (where appropriate and privacy-preserving), DAOs can improve their resistance to Sybil attacks, where a single entity creates multiple identities to manipulate voting or influence.
How they bridge: While SBTs are inherently non-transferable, their value for bridging lies in their ability to establish a persistent, verifiable on-chain history. A multi-chain DAO could issue specific SBTs on different chains, with each SBT attesting to a certain aspect of a member’s identity or contributions on that chain. Protocols could then be developed to “aggregate” or “interpret” these distributed SBTs to form a holistic view of a member’s standing across the entire multi-chain ecosystem. Zero-Knowledge Proofs (ZKPs) could play a crucial role here, allowing a user to prove possession of certain SBTs without revealing the underlying details.
Cross-Chain Messaging Protocols and Bridges
Dedicated cross-chain communication protocols and bridges are essential for the underlying technical infrastructure of credential bridging. These protocols allow information, including verifiable credentials or identity-related data, to be securely transmitted and verified across disparate blockchains.
- Examples: LayerZero, Wormhole, and similar interoperability solutions facilitate communication between chains.
- Role in Credential Bridging: These bridges would enable a DAO on one chain to query or receive proofs from another chain regarding a member’s credentials. For instance, if a DAO on Chain A requires a member to have a certain “governance participation score” from a DAO on Chain B, a cross-chain messaging protocol would facilitate the secure and verifiable transfer of this score.
Zero-Knowledge Proofs (ZKPs) for Privacy-Preserving Identity
ZKPs are a powerful cryptographic tool that allows one party (the “prover“) to prove to another party (the “verifier“) that a statement is true, without revealing any information beyond the validity of the statement itself.1
- Application in DAOs:
- Private Voting: A DAO member can prove they meet certain eligibility criteria to vote (e.g., hold a minimum number of governance tokens, possess a specific SBT) without revealing their exact token balance or the specific SBT.
- Selective Disclosure of Credentials: A user could prove they are over 18 without revealing their birthdate, or prove they reside in a specific country without revealing their full address. This is crucial for privacy-preserving KYC/AML solutions in DAOs.
- Reputation without Disclosure: A DAO could verify a user’s “reputation score” from an external reputation oracle without knowing the underlying activities that contributed to that score.
How they bridge: ZKPs can be used in conjunction with DIDs and VCs. A user holds VCs (e.g., a verifiable credential stating their active participation in DAO X on Ethereum). When they interact with DAO Y on Polygon, they can generate a ZKP that proves they hold the necessary VC without revealing the details of the VC itself, ensuring privacy while maintaining verifiable trust.
Architectural Considerations for Bridging Credentials
Implementing effective credential bridging for DAOs requires careful architectural design:
- Modular Architecture: Solutions should be modular, allowing DAOs to pick and choose the components that best suit their needs. This could involve a base layer for DIDs, alongside optional modules for SBTs, ZKPs, or specific cross-chain communication protocols.
- Standardization: Adherence to open standards (like W3C DIDs and VCs) is paramount for ensuring interoperability across different DAO ecosystems and blockchain networks.
- Decentralization at Core: While bridging mechanisms might involve some degree of centralization in their early stages (e.g., trusted relayers), the long-term goal should be to maximize decentralization to prevent single points of failure or censorship.
- User Control and Privacy: Users must retain full control over their identity and credentials. Privacy-preserving technologies like ZKPs are essential to prevent the leakage of sensitive personal information.
- Revocation Mechanisms: A robust system for revoking credentials (e.g., in cases of fraud, misconduct, or a change in status) is necessary. This can be challenging in decentralized environments but is critical for maintaining trust.
- Auditability and Transparency (where appropriate): While privacy is crucial, certain aspects of credential management, especially those related to governance power or compliance, may require a degree of transparency and auditability to ensure fairness and prevent manipulation.
Challenges and Future Directions
While the potential of bridging credentials for DAOs is immense, several challenges remain:
- Technical Complexity: Building secure and scalable cross-chain identity and credentialing solutions is technically challenging, requiring expertise in cryptography, distributed systems, and various blockchain protocols.
- Standardization Adoption: While standards exist, widespread adoption and consistent implementation across the diverse Web3 ecosystem are still evolving.
- Security Risks: Cross-chain bridges are often targets for exploits. Any credential bridging solution must prioritize robust security measures to prevent theft, manipulation, or unauthorized access to sensitive identity data.
- Scalability of ZKPs: While ZKPs offer significant privacy benefits, their computational overhead can be a barrier to widespread adoption, particularly for complex proofs. Ongoing research is focused on optimizing ZKP performance.
- Legal and Regulatory Clarity: The legal status of DAOs and decentralized identity remains ambiguous in many jurisdictions, adding a layer of uncertainty to the development and deployment of these solutions.
- User Education and Adoption: The concepts of DIDs, VCs, and SBTs can be complex for average users. Simplifying the user experience and educating the broader Web3 community are crucial for adoption.
- Sybil Resistance vs. Privacy: Striking the right balance between robust Sybil resistance and user privacy is a delicate act. Overly intrusive identity verification can undermine the ethos of decentralization.
- Governance Implications: How DAOs themselves will govern the issuance, revocation, and interpretation of bridged credentials will be a critical aspect of their evolution. This requires careful consideration of governance frameworks and dispute resolution mechanisms.
The future of DAO credentialing will likely involve a convergence of these technologies. We can anticipate:
- Evolving Identity Frameworks: More sophisticated decentralized identity frameworks that seamlessly integrate DIDs, VCs, and SBTs, allowing users to build a rich, portable digital identity.
- Specialized Oracles: The emergence of specialized “identity oracles” that can attest to off-chain credentials or aggregate on-chain reputation from various sources.
- Advanced ZKP Applications: Broader adoption of ZKPs for more complex privacy-preserving identity use cases, making it easier to prove attributes without revealing sensitive information.
- Interoperable Governance Tools: The development of governance tools that can interpret and act upon credentials originating from different chains, enabling truly multi-chain DAO operations.
- Reputation Marketplaces: The potential for marketplaces where verifiable reputation can be leveraged for various purposes, from enhanced lending terms in DeFi to preferential access in DAOs.
Final Thoughts
Managing bridging credentials is not merely a technical necessity for DAOs; it is a foundational pillar for their long-term success and the broader realization of Web3’s potential. By overcoming the fragmentation of identity and reputation across blockchains, DAOs can unlock unprecedented levels of interoperability, scalability, and collaboration.
The journey will be complex, fraught with technical and regulatory challenges, but the ongoing innovation in decentralized identity, soulbound tokens, cross-chain communication, and zero-knowledge proofs offers a clear path forward. As DAOs continue to evolve, the ability to seamlessly manage and bridge credentials will distinguish truly resilient and impactful decentralized organizations from their more isolated counterparts, paving the way for a more integrated, efficient, and equitable decentralized future.