How to Use Bridging Protocols Safely
How to Use Bridging Protocols Safely: A Practical Guide
The promise of decentralized finance (DeFi) is a world of borderless, permissionless value exchange. However, as the ecosystem has expanded from a single dominant chain to a sprawling multiverse of Layer 1s, Layer 2s, and sidechains, that value has become fragmented. To move capital from where it is to where the opportunity lies, users must cross “bridges.”
While bridging is a fundamental necessity for the modern crypto user, it remains one of the most perilous activities in the digital asset space. This guide provides a comprehensive framework for understanding how bridges work, the risks they entail, and the rigorous safety protocols you should adopt to protect your capital.
Introduction: Why Bridging Needs Extra Caution
In the early days of decentralized networks, Ethereum was essentially a walled garden. If you wanted to trade, you used Uniswap; if you wanted to lend, you used Aave. There was no need to worry about cross-chain compatibility because there was nowhere else to go. Today, the landscape is fractured across dozens of high-performance networks like Arbitrum, Optimism, Solana, and Avalanche. Bridging is the process of moving assets between these independent networks to access higher yields, lower fees, or exclusive applications.
Despite its utility, bridging is uniquely risky. In the traditional DeFi model, your primary risk is the smart contract of the protocol you are interacting with. When you bridge, however, you introduce a complex inter-chain dependency. You are not just trusting the destination protocol; you are trusting the bridge infrastructure that sits between two entirely different security environments. You are moving assets across a “no man’s land” where the rules of one chain may not apply to the other.
The history of crypto is littered with bridge catastrophes. From the $600 million Ronin Network hack to the $320 million Wormhole exploit and the $190 million Nomad bridge drain, bridges have earned the reputation of being the “most hacked sector in crypto.” This is because bridges represent massive “honeypots”—centralized points of liquidity that attract the world’s most sophisticated attackers. Unlike a single dApp, which might hold a few million in a specific pool, a bridge often holds the collective collateral for an entire ecosystem’s wrapped assets.
This guide is for the retail user, the yield farmer, and the active trader. It is designed to strip away the hype and provide a sober, practical methodology for navigating the cross-chain landscape without losing your principal.
How Bridging Protocols Work (Simple Mental Model)
To use a bridge safely, you must first understand that tokens do not literally “travel” across the internet from one blockchain to another. Blockchains are closed loops; an ETH token minted on Ethereum cannot exist natively on the Solana blockchain. Instead, bridging relies on accounting synchrony across two different ledgers.
The Lock-and-Mint Model
This is the most common mechanism used by bridges today. When you bridge 1 ETH from Ethereum to an L2, the bridge contract on Ethereum “locks” your native ETH in a vault. Once the bridge observes this lock, it sends a standardized message to the destination chain. The destination chain’s contract then “mints” a representative version of that ETH (often called Wrapped ETH or WETH). When you want to return, you “burn” the wrapped version on the destination chain, which triggers a message back to the origin chain to release the native ETH from the vault.
The Burn-and-Mint Model
Used primarily by protocols with native issuance on multiple chains (like Circle’s CCTP for USDC), this involves burning the asset on Chain A and minting an identical native asset on Chain B. This is generally considered safer because it avoids the creation of “wrapped” representations that rely on a central vault of collateral. However, it requires the token issuer to have a deep integration with both chains.
Liquidity Swaps
Some bridges function as cross-chain liquidity pools. Instead of minting new tokens, they maintain a pool of Native ETH on Chain A and Native ETH on Chain B. When you bridge, you give your ETH to the pool on Chain A, and a relayer gives you ETH from the pool on Chain B. These are often faster but rely heavily on the bridge having enough “rebalanced” liquidity on both sides.
Why Bridges Introduce Trust Assumptions
Every bridge relies on a “relayer” or a “validator” to witness the event on Chain A and confirm it on Chain B. The core question for any user is: Who is telling the destination chain that I actually deposited funds on the source chain? If that messenger is a single server or a small group of people, you are making a massive trust assumption. If the messenger is compromised, they can tell the destination chain that a deposit happened when it didn’t, allowing them to mint “fake” assets and drain the bridge.
Types of Bridging Protocols (and Their Risk Profiles)
Not all bridges are created equal. They fall into three primary categories, each with a distinct risk profile.
1. Native Chain Bridges
These are bridges built by the developers of the network itself. Examples include the Arbitrum Bridge, the Optimism Gateway, or the Polygon PoS Bridge.
-
Pros: They are generally considered the “gold standard” for security because they are deeply integrated into the network’s consensus. If the L2 fails, the native bridge is often the only way to recover funds.
-
Cons: They are often slow. For example, the official Arbitrum or Optimism bridges require a 7-day waiting period when moving funds back to Ethereum to allow for “fraud proofs.” They are also limited to moving assets between a specific L2 and its L1 parent.
2. Third-Party Bridges
These are independent protocols like Stargate, Across, Hop, or Synapse. They often use liquidity pools or intent-based models to facilitate near-instant transfers.
-
Pros: High speed, lower fees, and excellent user experience across many different chains (e.g., moving directly from Avalanche to Arbitrum).
-
Cons: You are trusting a third-party smart contract and their specific security model. If the protocol’s private keys are leaked or its liquidity is drained, your funds in transit are at risk.
3. Canonical vs. Non-Canonical Assets
A “canonical” asset is the official version of a token recognized by a network (e.g., the USDC issued by Circle). A “non-canonical” asset is a wrapped version created by a specific bridge (e.g., “Wormhole-wrapped USDC”).
-
The Risk: This is a critical distinction. If you use “Bridge X” to move USDC to a new chain, you receive “Bridge X-USDC.” If “Bridge X” is hacked, your “Bridge X-USDC” could become worthless because the collateral backing it has been stolen, even if the USDC on the origin chain is fine. Always aim to hold canonical assets whenever possible, especially for long-term storage.
Common Bridging Risks You Must Understand
To bridge safely, you must recognize the specific attack vectors that have led to billions in losses over the last few years.
Smart Contract Vulnerabilities
Since bridges hold massive amounts of locked assets, even a tiny logic error in the code can lead to a total drain. The Nomad hack occurred because of a flaw that allowed users to withdraw funds without a valid proof, simply by copy-pasting a successful transaction string. Because the bridge didn’t properly validate the “root” of the message, hundreds of people were able to replicate the hack manually.
Validator or Multisig Compromise
Many bridges are secured by a “multisig”—a group of people or servers that must sign off on transactions. If an attacker gains control of the majority of these keys, they can authorize the withdrawal of all funds in the bridge vault. The Ronin Bridge hack was the result of an attacker gaining access to four Sky Mavis validators and one third-party validator, enough to hit the 5-of-9 threshold required to drain $600 million.
Oracle and Message-Passing Failures
Bridges rely on “oracles” to tell them the state of the other chain. If an oracle is manipulated or provides false data, the bridge may mint assets that have no collateral backing them. This is often an issue with “wrapped” assets that rely on price feeds to maintain their peg.
Liquidity Risk and Stuck Funds
Third-party bridges rely on liquidity providers. If you try to bridge a large amount and there isn’t enough liquidity on the destination side, your funds may become “stuck.” While your funds aren’t necessarily “stolen,” they are inaccessible until more liquidity is added or the transaction is manually resolved by the bridge team, which can take days or weeks.
Chain Reorgs and Finality Issues
Blockchains occasionally undergo “reorgs” where recent blocks are discarded. If a bridge processes your transfer before the source chain transaction is “final,” and that transaction is later reverted, the bridge has effectively given you money for free on the destination chain. This creates a hole in the bridge’s balance sheet, which can lead to insolvency.
Front-end Attacks
Sometimes the bridge’s code is fine, but the website you use to interact with it is hacked. Attackers can inject a script into the website that changes the destination address of your bridge transaction to their own address. You think you are bridging to your own wallet on Solana, but you are actually sending it to the hacker.
How to Evaluate a Bridge Before Using It (Checklist)
Before you connect your wallet to a new bridge, run through this practical checklist to determine if the protocol is worth the risk.
1. Security Track Record
Has the bridge been exploited before? A previous hack isn’t necessarily a dealbreaker—many protocols become more resilient after an incident—but pay attention to the post-mortem. Did the team reimburse users? Did they fix the underlying architecture, or was it a “band-aid” fix? Avoid bridges with a history of “lucky” saves or opaque security practices.
2. Audits and Bug Bounties
Look for audits from reputable firms like OpenZeppelin, Trail of Bits, or Spearbit. However, remember that an audit is a “snapshot” in time. If the bridge has updated its code since the last audit, that audit is largely irrelevant. A robust, active bug bounty program (like those hosted on Immunefi) is often a better signal, as it incentivizes ethical hackers to find and report flaws before criminals can exploit them.
3. Decentralization and Trust Assumptions
Check the “L2Beat” or “BridgeBeat” rankings. How many signers are required to move funds? Is it a 2-of-3 multisig (extremely risky) or a decentralized network of 100+ validators (safer)? The more centralized the bridge, the higher the risk of censorship or theft. If a bridge is controlled by a single company, you are not using DeFi; you are using a centralized service with a web3 interface.
4. TVL and Usage
Total Value Locked (TVL) is a double-edged sword. High TVL means there is plenty of liquidity for your trades, but it also makes the bridge a more attractive target for hackers. Look for a healthy balance: a bridge that has handled billions in volume over a long period of time is generally more “battle-tested” than a brand-new bridge with a high TVL driven by a speculative airdrop.
Step-by-Step: How to Bridge Assets Safely
This is the operational workflow you should use for every bridge transaction, regardless of the amount.
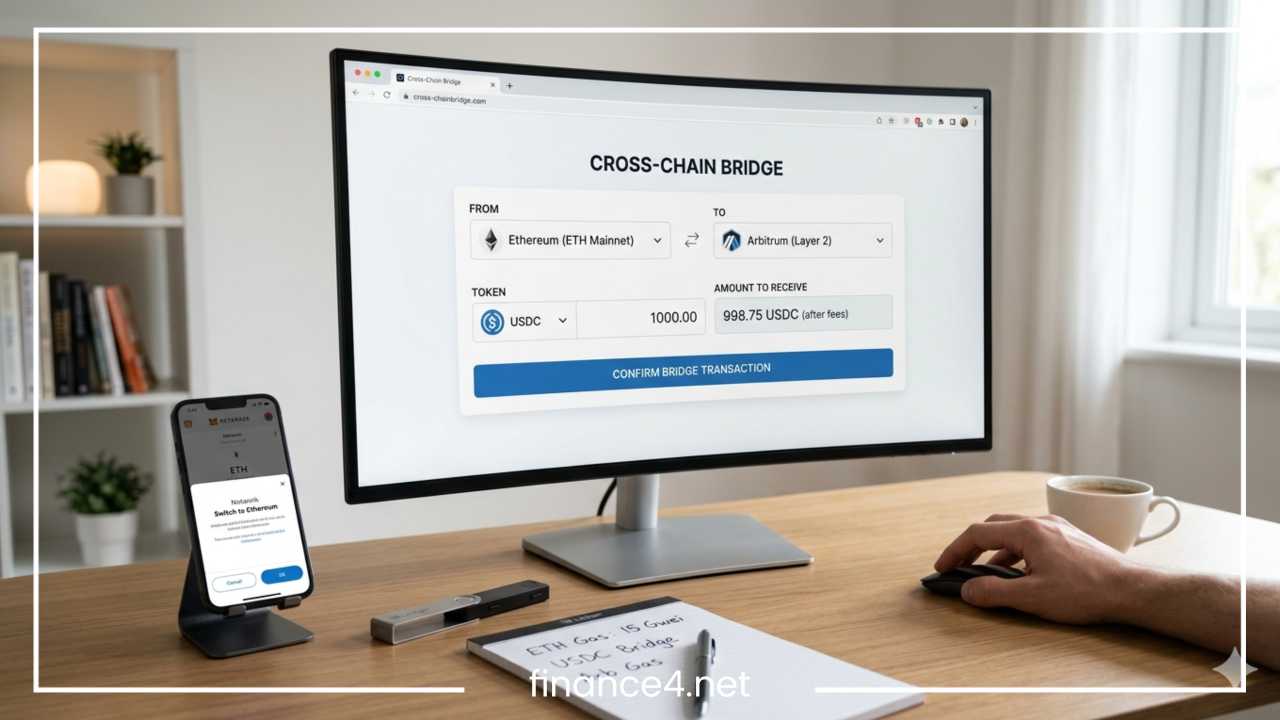
1. Start with a Small Test Transaction
Never bridge your entire position at once. Send the minimum amount allowed first. Verify that it arrives on the destination chain and that the resulting token is the “canonical” version you expected. If the test transaction fails or is delayed for hours, you’ve only lost a small amount of gas and time, rather than your life savings.
2. Double-Check URLs and Contracts
Phishing is the most common way retail users lose money.
-
Bookmarks: Bookmark the official links from the project’s official X (Twitter) profile or a trusted aggregator like DefiLlama. Never click “sponsored” links at the top of Google Search results.
-
Contract Review: Before clicking “Approve” in your wallet, look at the contract address. If your wallet (like MetaMask or Rabby) flags the contract as “new” or “unverified,” stop and investigate.
3. Verify Destination Details
Ensure you have already added the destination network to your wallet. Sometimes users bridge funds to a network they haven’t configured, leading to a “panic” when they don’t see their funds. Verify that the token address on the destination chain matches the official token address (check Coingecko or the chain’s official explorer).
4. Watch Confirmations
Most bridges will show a progress bar indicating “Source Confirmation,” “Relayer Processing,” and “Destination Confirmation.” Stay on the page until all steps are green. If a transaction hangs at “Relayer Processing,” copy the transaction hash immediately. This is your proof of deposit if you need to contact support.
5. What to Do If Funds Are Delayed
If the bridge UI says “Successful” but you don’t see the funds:
-
Check the block explorer for your destination address. It’s possible the UI is lagging but the funds are there.
-
Ensure you have enough gas on the destination chain to actually use the funds once they arrive. Many users bridge ETH to a new chain but don’t have the native gas token of that chain to move it.
6. When NOT to Retry
If a transaction fails, do not immediately try again. Check the bridge’s social media or status page. If the bridge is undergoing a technical failure, retrying will only lead to more funds getting stuck or lost in the same “clogged” pipe.
Operational Security Best Practices
Zooming out from the bridge itself, your personal security habits are your last line of defense.
Use Hardware Wallets
Always initiate bridging transactions from a hardware wallet like a Ledger, Trezor, or Lattice. This ensures that even if your computer is compromised by “clipper” malware (which changes addresses in your clipboard), you have to manually verify the address on the device’s screen before the transaction is sent.
Separate “Hot” and “Cold” Wallets
Never bridge directly from your “vault” wallet—the one where you keep your long-term holdings. Instead, move the specific amount you want to bridge to a “burner” or “hot” wallet. Use that hot wallet to interact with the bridge. Once the funds arrive on the destination chain, move them to a secure address on that chain. This “air-gapping” of your main funds protects you if the bridge has a “drainer” vulnerability.
Revoke Permissions
Many bridges require you to “Approve” an infinite amount of a token so they can pull funds for the transfer. If that bridge is later hacked, the attacker can use that “infinite approval” to drain your wallet, even if you aren’t currently using the bridge. Use tools like Revoke.cash or the built-in approval managers in Rabby wallet to clear these permissions immediately after your bridge transaction is confirmed.
Avoid Public Wi-Fi
Bridging involves sensitive data and wallet signatures. Never perform these actions on public, unsecured networks where “man-in-the-middle” attacks can intercept your traffic or redirect you to a malicious front-end.
Risk Management Strategies for Bridging
Professional risk management is what separates survivors from victims in the crypto space.
1. Never Bridge More Than You Can Afford to Lose
This is the golden rule of crypto, but it is doubly true for bridging. Because you are trusting an intermediary protocol, there is always a non-zero chance of a total loss. Keep the majority of your net worth in “native” assets on secure Layer 1s or in cold storage.
2. Break Large Transfers into Chunks
If you need to move $100,000, don’t do it in one go. Break it into four $25,000 transfers. While this costs more in gas fees, it ensures that a single bridge failure or exploit doesn’t wipe out your entire capital. Think of the extra gas as an “insurance premium.”
3. Avoid Bridging During High Volatility
During market crashes or massive pumps, bridging is dangerous. Networks become congested, gas fees spike, and bridge liquidity can dry up instantly as everyone rushes for the exits. Bridges are most likely to break or become insolvent when the market is at its most chaotic.
4. Diversify Your Bridge Usage
Don’t rely on a single third-party bridge for all your needs. If you regularly move funds, use two or three different reputable bridges. If one is exploited, you only have a fraction of your “in-transit” capital at risk.
What to Do If Something Goes Wrong
If you find yourself in a situation where your funds have left the source chain but haven’t appeared on the destination chain, stay calm.
Stuck Transactions
99% of “lost” funds are actually just stuck. Check the bridge’s Discord or Telegram. Usually, there is a “re-submit” or “claim” button on the bridge UI that can be triggered if the relayer missed the initial event. You may need to provide the transaction hash from the source chain.
Bridge UI Down
If the bridge’s website goes offline while your funds are in transit, don’t panic. The smart contracts still exist on the blockchain. Most major bridges have a “manual withdrawal” process that can be initiated directly through the block explorer (like Etherscan) if you are technically proficient.
Avoiding Scam “Support”
This is the most dangerous part of the process. If you ask for help on X (Twitter) or Discord, you will be flooded with “support bots” or “help desk” accounts offering to “synchronize your wallet.” These are all scams. No legitimate bridge support will ever ask for your seed phrase or ask you to connect your wallet to a “fixer” website.
The Future of Bridging and Safer Alternatives
The industry knows that bridging is a problem, and a new generation of “safer” interoperability is emerging.
Intent-Based Bridges
New protocols (like Across or UniswapX) use “intents,” where you express a desire (e.g., “I want 1 ETH on Base”), and a sophisticated market maker fulfills that request for you instantly. You only release your funds once they have proved they sent the money to you. This shifts the technical risk away from the user and onto professional “solvers.”
Native Interoperability
Systems like the Cosmos Inter-Blockchain Communication (IBC) protocol allow chains to talk to each other natively without a third-party bridge. As Ethereum rollups become more integrated, we will see more “shared sequencer” models that make bridging feel like a simple internal transfer.
Using CEXs as a Bridge
Sometimes, the safest “bridge” is a Centralized Exchange (CEX) like Coinbase or Binance. If you want to move funds from Ethereum to Solana, it is often cheaper and safer to send ETH to a CEX, trade it for SOL, and withdraw it to your Solana wallet. While this involves “Know Your Customer” (KYC) requirements, it avoids the smart-contract “honeypot” risk of a bridge.
Final Thoughts: Bridging Is Powerful, Not Risk-Free
Bridging is a remarkable technological feat that allows the fragmented world of crypto to function as a unified economy. It provides you with the freedom to chase opportunities wherever they arise. However, that freedom comes with a significant burden of personal responsibility.
The “practical guide” to bridging can be distilled into a single mindset: Verify, don’t trust. Treat every bridge as a temporary tunnel through a dangerous mountain. You want to spend as little time inside the tunnel as possible, carry only what you need, and ensure you have a map of the exits. By following the checklists and operational security measures outlined in this guide, you can navigate the multi-chain future with confidence.